
Onno (VK6FLAB)
Anything and everything Amateur Radio and beyond. Heavily into Open Source and SDR, working on a multi band monitor and transmitter.
#geek #nerd #hamradio VK6FLAB #podcaster #australia #ITProfessional #voiceover #opentowork
- 13 Posts
- 77 Comments


We know very little beyond:
- It will go live on 10 December 2025
- There will be heavy fines.
- Government ID is not allowed to be the only method.
- A self declaration (tick box) is insufficient as a check.
There are to my knowledge no third party providers approved for this legislation. The process to assess actual implementation details started in July 2025, and the results thus far are underwhelming to put it mildly, you might call it a shitshow.
Below is the official sum total of what we know, most of it motherhood statements and “coming soon”.
https://www.esafety.gov.au/about-us/industry-regulation/social-media-age-restrictions
Media commentary wants to “protect the children”, but have no idea how you might do so, let alone consider the implications or implementation details.
Source: I’m an ICT professional with 40+ years experience.


- •
- 3M
- •
What are you attempting to achieve by opening this list of urls?
What is the difference between running this script and setting this list as either a bookmark, or the homepage in your browser?
What does your network have to do with the reachability of these sites?
If you’re managing the privacy of your own network, why are you not monitoring those services?
Keep your existing phone and OS.
Use it differently. Decide what information you store on it, which applications you install or disable, what permissions you grant and what services you use.
Just installing an OS to “debloat and degoogle” is not ever going to change anything unless you change your habits and you don’t need to change OS to do that.


Yeah … that thought occurred to me as well.
I wonder if there’s a way that you can legally monetize the process, so the organisation who left a gaping hole … or several bazillion in this case … gets an education in corporate security and the researcher gets paid for their efforts. A corporate symbiosis if you like.
If course the non legal way is extortion … but that tends to go towards warfare and mutually assured destruction, rather than collaboration.
Perhaps this opens the door to a white hat penetration testing department at the corporate regulator who issues fines (which pay for the work) … but I’m not seeing any evidence of an appetite for anything even remotely resembling such a set-up anywhere on Earth.
Espionage on the other hand …
I’m not a Telegram user, but the internet says: https://www.ticktechtold.com/export-telegram-chat-messages/


I only noticed the € vs $ because I was searching for the case, so all good.
It’s telling that they continue to attract fines. I saw the ones you mentioned also but didn’t have the energy to start digging.
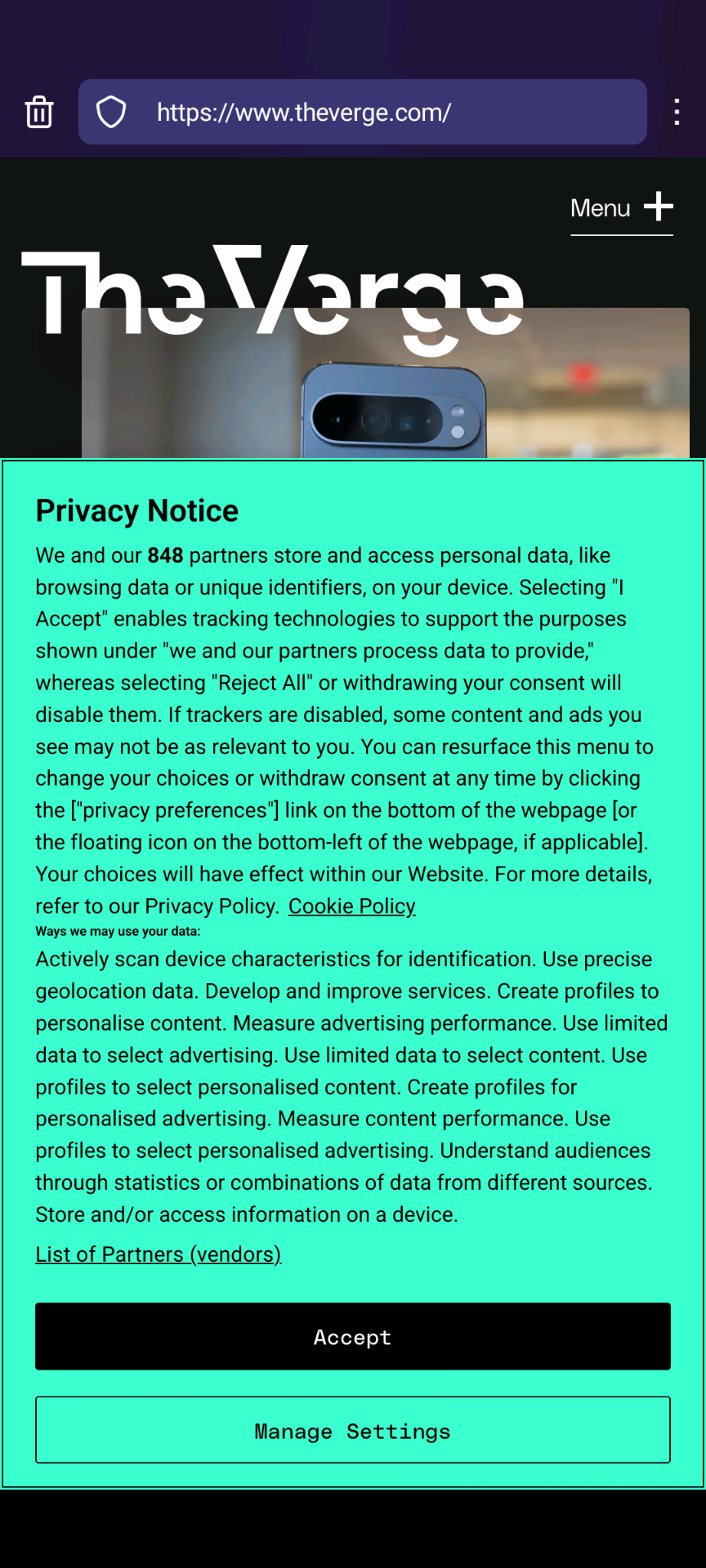
Despite assertions made to the contrary in this thread, I’m not at all convinced that they’re doing anything other than maximising shareholder value to the exclusion of all other considerations, including making a risk assessment in relation to paying fines versus compliance with the law.


Again, you vastly underestimate the size of Meta.
In the last quarter of 2024 it shows a net income of $20,838 million. A $20 million fine would change that 3 into a 1 and again, that’s net income for just for three months.


Think about it in terms of risk / reward or if you like, shareholder value.
If the value of the data exceeds the fine combined with the risk of it being discovered, the data will continue to exist.
Factor in the cost of actually guaranteeing that deleting something across all online, nearline, offline and archived data stores and the chances of anything being purposely deleted are not high.
Accidental data loss, sure, purposeful data loss, I can’t see it happening.
On Android I use FBReader. I paid for the Premium version.


You don’t need to.
By using metrics like IP address , age, gender, race, religion, city, workplace, application, website, favourite song, colour and flavour, throw in a few more questions and you can lucratively target specific groups of people.
By COMBINING those metrics you can target extremely small groups of people, groups with precisely ONE member.
No need for a unique GUID at all.


I hear you, but in the last year I’ve begun wondering if full public disclosure isn’t a better way to go these days.
The sheer volume of breaches is overwhelming and in my experience (of over 40 years as an ICT professional) many companies sweep their failures under the carpet, hide behind crisis management teams and marketing speak, and ridicule those bringing issues to their attention.
Their disclosure is abysmal if it’s made at all and there are precious few who reveal precisely what data was exfiltrated or how the issue was remediated.
This way anyone can verify the issue and companies cannot hide, everyone sees precisely what’s leaked and can act accordingly.
If you know of a more effective way, I’d love to hear it.
So far the Wayland implementation requires embedded X11 which puts everything in the same environment again.
I’ve not yet discovered how to run separate Wayland screens across the network from a Docker container and I’m also not sure if either Chrome or Firefox actually support native Wayland, from memory they didn’t last time I checked.


- •
- 1Y
- •


- •
- 2Y
- •




1/1/1