I remember a while back, years before this surfaced, there was a thread on /g/ with a group photo of Balena’s employees and a caption like “why does it take so many people to develop an electron wrapper around dd”. Obviously it was low effort engagement bait (balena does much more than etcher), but the comments were full of people calling the company a glowie honeypot and the like. Moral of the story: Trust the schizos, they sense spyware form lightyears away.

But being too rigid with letting stupid opinions of a project’s founder cause you to reject everything, would have you miss the big-picture benefits of having such a project exist
That’s the truth. The reason online “communities” constantly argue and never get anything done is because everyone is focused on not doing the wrong things that they forget about doing the right things. A while ago I saw a post making fun of some chuds who compiled a list of “woke” video games that they wanted to boycott. The people in this thread deciding to leave proton because its ceo said something positive about trump once don’t strike me as much different.
You can lock your password database with a key file (this is a standard feature in keepassxc) and transfer the key file once between devices via sneakernet (microsd or usb drive). That way even if someone intercepts your database file, AND knows your password, it is still virtually impossible to crack. Should be a good enough solution, unless you are quantum-tier paranoid
If you’re on Linux and you like minimalism, pass is also a great option

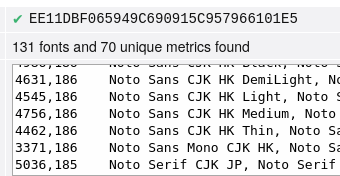
Okay, I just tested Tor on windows, and it shows a bunch of microsoft fonts that my linux box doesn’t have.
But what I did notice is that the fingerprint changed on my linux box after a full restart of tor browser. So I guess their approach is to randomize fingerprints between sessions, rather then to keep everyone’s fingerprint the same?

how much of the internet is unusable with js disabled
Quite a lot actually. A lot of articles / blogs / news sites are actually more usable without javascript than with, because none of the annoying popups and shit can load. I suggest having two browser profiles: one with javascript enabled by default, and one with javascript disabled. So for things like online shopping, you’d open the js profile. And for things where you expect to do a lot of reading, use the nojs profile. Ublock origin also lets you temporarily enable/disable js for a particular website pretty easily.

I’m slowly starting to agree with @ssm that safeguarding against fingerprinting is an exercise in futility though…QubesOS sounds like something that might help though, since it makes it easy to browse from a virtual machine with fonts and other settings that may be leaked set to the most bog-standard defaults.
On a related note, disabling javascript can actually improve your user experience quite a lot for certain types of tasks. A lot of news/blogs/article-style websites nowadays are actually more usable without javascript, because you don’t have to waste time closing all of the ads and cookie popups. I have a separate browser profile with js disabled and use it quite a lot.
“The fuck else were these people expecting” is also my visceral reaction whenever shit like that happens, but if I think about for a bit longer, I realize that it’s not much different than saying “The fuck else were you expecting” to a rape victim who went alone into a dark alley. Sure, people are stupid for engaging with this obvious scam, but the bad guy is still the scammer, not the victims.